The Zero Trust Mindset: Engineering Security as an Architecture, Not a Product
Zero Trust is a concept mentioned in almost every security presentation today. However, when we look at its implementation in the field, we often see it applied in the wrong place, with wrong expectations, and using the wrong tools. The main reason for this is that Zero Trust is positioned as a technology or a purchasable product. In reality, Zero Trust is not a licensed, boxed, or vendor-specific solution. It is an architectural perspective and, more importantly, a mindset.
The essence of Zero Trust is clear: Never trust, always verify. Do not implicitly trust any user, any device, or any connection. Trust is a state that must be continuously re-earned. This approach completely eliminates the classic “inside is safe, outside is dangerous” assumption. Because in the modern IT world, inside and outside are no longer separated by clear boundaries.
In summary:
- Zero Trust is an architectural approach, not a product
- It rejects the concept of implicit trust
- It is based on continuous verification
This article is part of a series that treats IT infrastructure as a system. For the starting point: IT Infrastructure Is Not a Collection of Products
Zero Trust Belongs to No Vendor
Zero Trust began taking shape through the visions of security vendors. However, an important distinction must be made: Zero Trust is not a concept “owned” by any vendor. It cannot be represented by a single technology.
The reason is this: Zero Trust requires multiple layers to work together consistently and simultaneously. If network, security, identity, user, device, and application layers operate in silos, Zero Trust remains only a narrative. It has no architectural counterpart.
Key points:
- Zero Trust does not belong to any vendor
- It cannot be built with a single technology
- Cross-layer consistency is required
User and Device Verification: Where the Architecture Begins
Zero Trust architecture starts with a fundamental question:
“Should this user and this device actually have access to the resource they are trying to reach right now?”
To provide a meaningful answer, the first step is verifying the users and devices joining the network. Active Directory, LDAP, or modern identity providers sit at the center of this structure. What resources a user can access is determined not only by their identity but also by their role and risk posture.
But from a Zero Trust perspective, it is not only about who the user is — the device’s status, whether it belongs to the corporate inventory, and its compliance with security policies are all part of this decision.
Key takeaways:
- User verification alone is not sufficient
- Device identity and posture are also evaluated
- Access decisions are context-driven
VPN ≠ Zero Trust: The Right Framework for Remote Access
Remote work is no longer the exception — it is the standard. Yet many organizations still operate with classic VPN logic: the user connects to VPN and instantly becomes part of the entire local network. This is not Zero Trust. This is simply remote access.
In a Zero Trust architecture, remote access does not mean “access to everything.” The user only accesses the applications or resources they are authorized for. The goal is always the same: minimize access and continuously verify it.
Key points:
- VPN ≠ Zero Trust
- Access should be to the resource, not the entire network
- Authorization is continuously verified
Continuous Verification and MFA
What distinguishes Zero Trust from classic security approaches is that authentication is not treated as a one-time event. As user and device behavior changes, access is continuously re-evaluated.
This is where Multi-Factor Authentication (MFA) comes in. Additional layers such as SMS, mobile app notifications, hardware tokens, or biometric verification are used. Especially for critical applications like mail servers, financial systems, or ERP, users are required to re-verify themselves at regular intervals.
In summary:
- Verification is continuous
- MFA is a core component of Zero Trust
- Intervals are shortened for critical resources
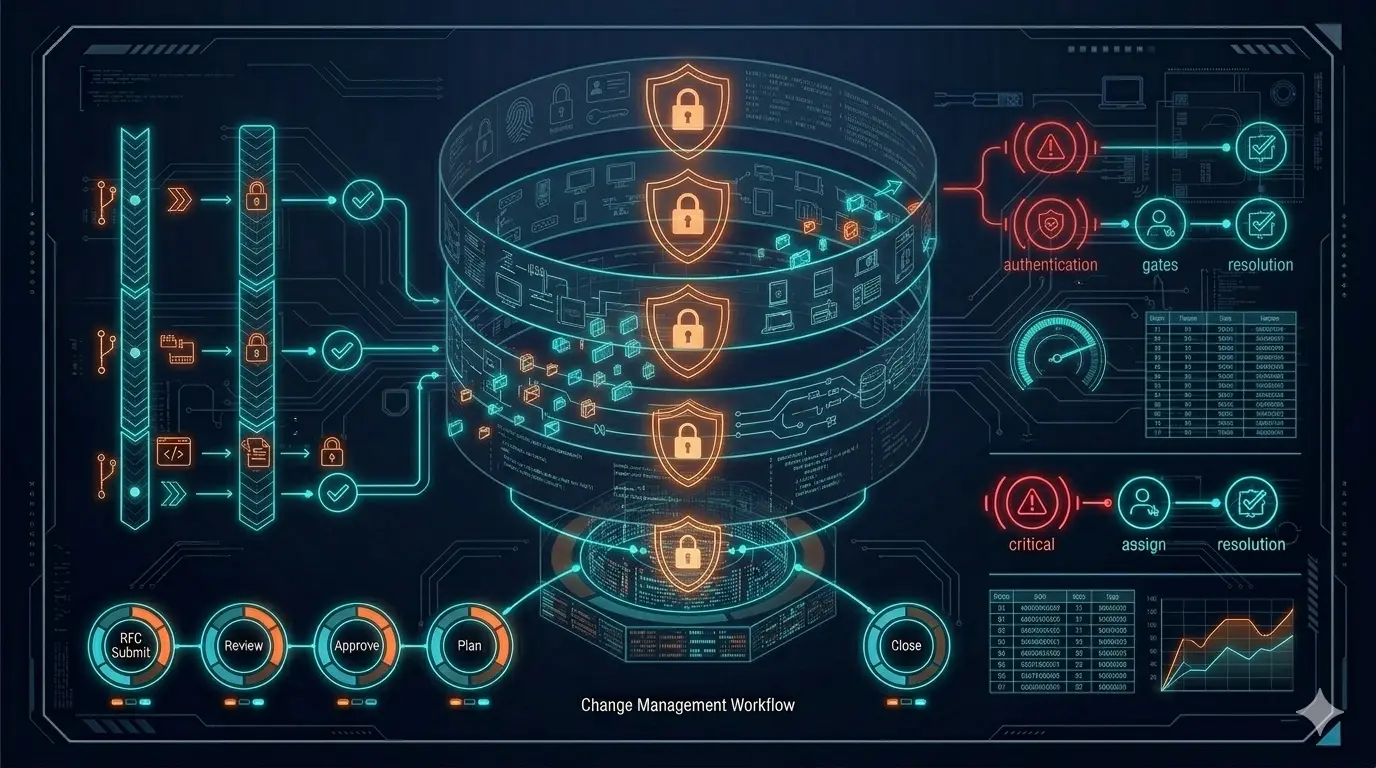
Firewall: The Policy Decision Point
The firewall layer plays a central role in Zero Trust architecture. But this role goes far beyond the classic “device that controls internet egress.” In the Zero Trust approach, the firewall is a decision point with identity and context awareness.
Rules defined on the firewall should not be based solely on IP or port. When user-, group-, and application-based rules can be written, Zero Trust becomes truly implementable.
To understand how switches, firewalls, and APs work together: Switch, Firewall, AP — Why Choosing the Right Products Is Not Enough
This layer in summary:
- Firewall is the policy decision point
- Identity and application awareness are essential
- Port-based rules are not sufficient
The Access Layer: Where Zero Trust Starts
Zero Trust is not only applied at the firewall and VPN layers. The access layer is where the architecture begins. 802.1X and NAC solutions come into play here. All switch ports and wireless access are controlled by a central system. Users or devices are verified before joining the network, and based on this verification, VLANs are dynamically assigned or policies are applied.
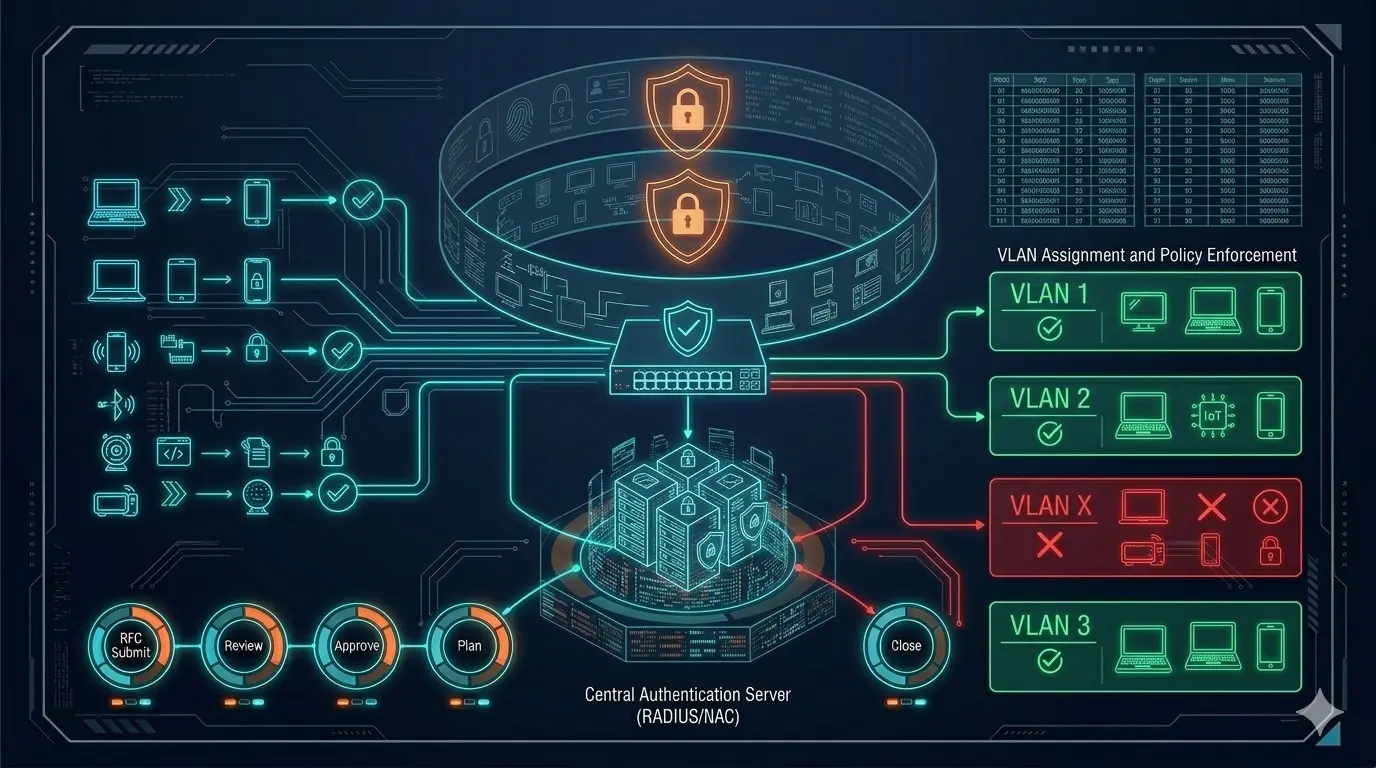
Key points:
- Zero Trust starts at the access layer
- 802.1X provides centralized control
- Static VLAN / SSID structures do not scale
Device Profiling and IoT
In modern Zero Trust architectures, not only user devices but all endpoints connecting to the network are brought under control. Printers, cameras, IP phones, card readers — all are included in the verification process.
Next-generation NAC solutions combine multiple parameters such as DHCP fingerprint, CDP/LLDP information, and device manufacturer data to perform device profiling. Whether the device is up to date, its security posture, and compliance with corporate standards are all evaluated.
Key points:
- Device profiling is critically important
- MAC address alone is not sufficient
- Inventory integration is essential
Guest Access: Trust Is Never Assumed
Even guest access is controlled in Zero Trust architecture. Guest users are verified through guest portals and are granted access only for a specific duration and with specific permissions. Guests can typically only access the internet; their access to company resources is restricted.
In summary:
- Guest access is not unlimited
- Time- and permission-based controls are applied
- Trust is never assumed
Continuous Monitoring: The Most Critical Part of the Architecture
Access and behavior are monitored and logged at every layer. If an anomaly or risky activity is detected, the system automatically restricts access or requests additional verification.
For building real visibility into your infrastructure: The Monitoring Mindset: Not Just Seeing, But Understanding and Acting Proactively
Conclusion
Zero Trust is not a product. It cannot be built with a single device. You cannot say “we implemented it, we’re done.”
Zero Trust is a living architecture in which firewall, switch, and wireless infrastructure work together by drawing user and device information from a central point, with access being re-questioned at every stage. That is why Zero Trust should be seen not as a technology to be purchased, but as a capability to be designed and operated.
Note
This article was originally introduced on Substack in a shorter, narrative form. This version expands the architectural foundation for the series.
👉 Read the article on Substack: Click Here
Related Articles
Architecture & Security Design
- 📐 IT Infrastructure Is Not a Collection of Products — The foundational article of this series
- 🏗️ Switch, Firewall, AP — Why Choosing the Right Products Is Not Enough — Systems thinking in core network design
- 📊 The Monitoring Mindset: Not Just Seeing, But Understanding and Acting Proactively — Building real visibility into your infrastructure
Technical Engineering
- 🔐 Unlocking Success in 802.1X Projects: Field Insights — Identity-based access in enterprise networks
- 🛡️ Network Packet Broker (NPB) Masterclass — Advanced traffic visibility and security strategy
- 🛠️ The Backdoor of the Network: Next-Gen Console Server Architecture — Out-of-band access when everything else fails
