802.1X Projects: Deploying the Identity-Based Architecture in the Field
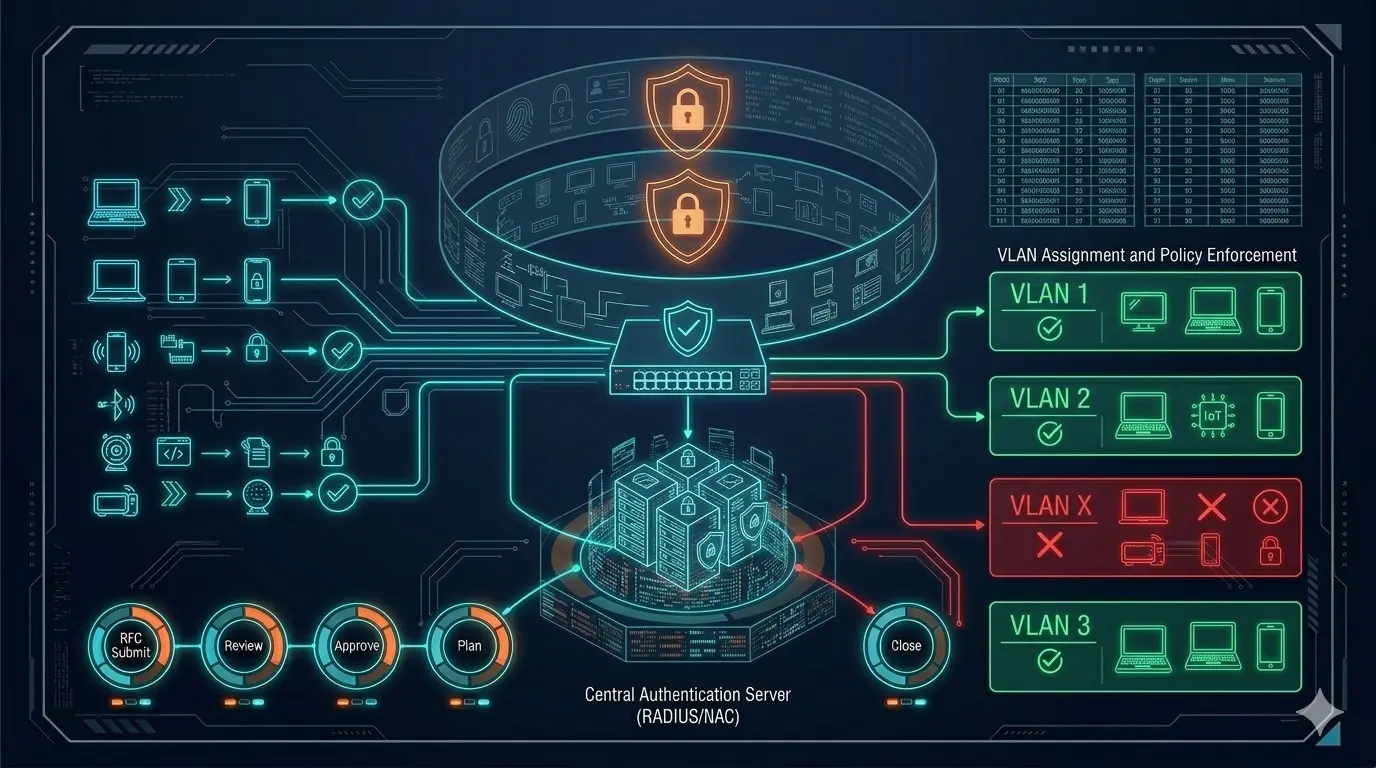
802.1X Projects: Deploying the Identity-Based Architecture in the Field 802.1X projects look like a network job from the outside; because the points of contact are switch ports, SSIDs, and RADIUS. But in real life, the success of 802.1X is often determined not on the network devices, but in the Active Directory structure, the certificate infrastructure (PKI), and endpoint management. The reason is simple: 802.1X forces the organization to talk about its “identity model” rather than just the port’s VLAN. In other words, you transition from “which port belongs to which VLAN” to a system of “which identity enters the network with what authority.” ...
