F5 BIG-IP Is Not a Load Balancer — It’s an Application Delivery Platform
The most common introduction to F5 in an enterprise goes like this: someone opens a ticket that says “the load balancer is down” and points at the F5. The problem is already in that sentence.
F5 BIG-IP is not a load balancer. Calling it one is like calling a data center a server room — technically not wrong, but it completely misses the point.
F5 BIG-IP is an Application Delivery Controller (ADC): a full-proxy platform that manages, secures, optimizes, and makes applications highly available across local and global infrastructure. Load balancing is one of perhaps a dozen things it does.
How to Read This Series
This article gives you the big picture — what F5 is, where it sits, what each module does, and when it makes sense over alternatives.
If you are a network or security engineer who wants to go deep into configuration, iRules, migration field notes, and architecture details — jump directly to the module that interests you:
- 🔧 F5 LTM Deep Dive — Virtual servers, pools, iRules, SSL offloading, HA, and a 30-device migration walkthrough
- 🌐 F5 GTM & GSLB Deep Dive — iQuery, Wide IPs, topology routing, DNS TTL strategy, multi-DC failover design
- 🛡️ F5 WAF Deep Dive — ASM vs Advanced WAF, OWASP Top 10, bot defense, transparent-to-blocking deployment strategy
If you are an architect or decision-maker evaluating whether F5 fits your infrastructure — keep reading here. This article answers that question without requiring you to understand iRule syntax.
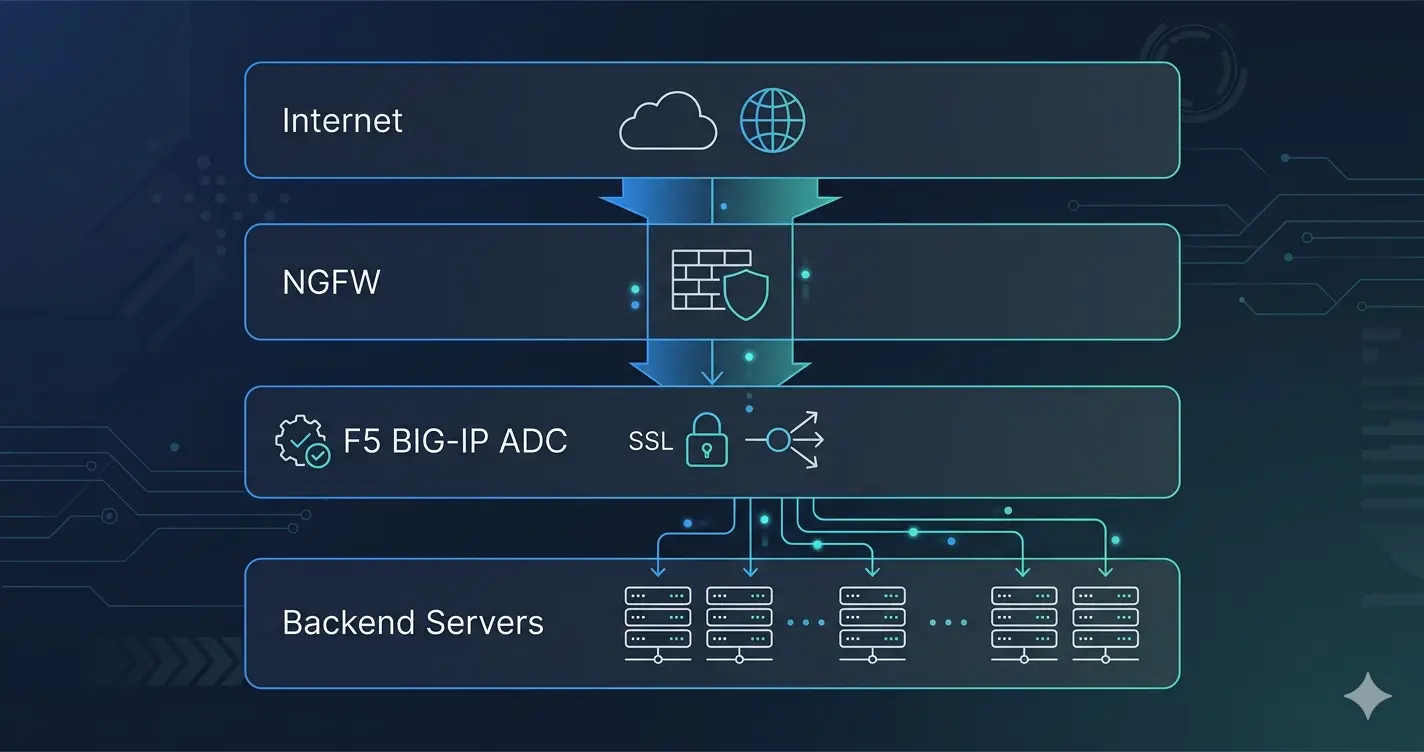
Where Does F5 Sit in Enterprise Architecture?
F5 BIG-IP operates between the firewall and the application servers:
Internet
│
[DDoS Scrubbing / ISP]
│
[NGFW — Palo Alto / Fortinet] ← L3/L4: routing, IP filtering, VPN, stateful inspection
│
[F5 BIG-IP] ← L4–L7: application delivery, SSL, health, routing logic
│
[Backend Servers / App Clusters]
The firewall handles network-level decisions. F5 handles everything above that layer — SSL termination, health-aware load balancing, session persistence, traffic manipulation, and Layer 7 security.
This separation matters because a firewall is not designed to do what F5 does. It cannot efficiently terminate thousands of SSL sessions per second, inspect HTTP response bodies for health monitoring, rewrite application headers on the fly, or make routing decisions based on URI paths, cookies, or user identity.
In a dual data center design, the architecture expands:
[F5 GTM] ← DNS-level: directs clients to the right DC
/ \
[DC-1] [DC-2]
[F5 LTM] [F5 LTM] ← Local: distributes traffic within each DC
│ │
App Servers App Servers
GTM sits above both LTMs and answers DNS queries — directing clients to the appropriate data center based on health, load, and geography. This is what makes multi-DC failover automatic rather than manual.
The Full Module Map
TMOS (Traffic Management Operating System) is the foundation. Every F5 module runs on top of it. Understanding which module solves which problem is the key to both architecture design and licensing conversations.
LTM — Local Traffic Manager
The core module. Almost every F5 deployment starts here.
LTM is a full-proxy ADC: it terminates every client connection, inspects it, makes routing and policy decisions, and opens a new connection to the backend. This full-proxy position gives complete visibility and control over application traffic.
What LTM provides:
- Load balancing across pools of backend servers — with health monitoring that understands application responses, not just TCP reachability
- SSL/TLS offloading — terminating HTTPS on behalf of backends, removing their encryption burden
- Session persistence — keeping users connected to the same backend server across requests
- iRules — a programmable scripting layer that manipulates traffic at wire speed: rewrite headers, route by URI, inject content, enforce rate limits
- High availability — Active-Standby or Active-Active clustering with sub-second failover
→ F5 LTM Deep Dive: Virtual Servers, iRules, SSL Offloading & HA
GTM / DNS — Global Traffic Manager
LTM manages traffic within one data center. GTM manages traffic between data centers — at the DNS level.
When a client resolves webapp.company.com, GTM answers the DNS query. Its answer depends on which data center is healthy, what the current load is, and where the client is geographically located.
GTM’s key capability is iQuery — a proprietary protocol that gives it real-time application health data directly from LTM. When a backend application fails and LTM marks its pool down, GTM knows immediately and stops routing new clients to that data center — without waiting for DNS TTL expiry.
What GTM provides:
- Global Server Load Balancing (GSLB) across multiple data centers
- Automatic DNS-level failover when a DC goes offline
- Topology-based routing — European users to EU data centers, Middle Eastern users to regional DCs
- Flexible policies: always-prefer-primary (Global Availability), equal distribution (Round Robin), or connection-aware (Least Connections)
→ F5 GTM & GSLB Deep Dive: Global Traffic Management and DNS Failover
WAF — Web Application Firewall (ASM / Advanced WAF)
A network firewall operates at L3/L4. It cannot inspect whether a POST request body contains a SQL injection payload. WAF can.
F5 WAF sits inline on the LTM virtual server, inspecting HTTP/HTTPS application traffic after SSL termination. This positioning gives it full visibility into decrypted content.
F5 offers two WAF tiers:
- ASM — signature-based protection against known attacks, OWASP Top 10 coverage, parameter and cookie enforcement
- Advanced WAF — adds behavioral bot defense, credential stuffing protection, JavaScript challenges, and L7 DoS mitigation
What WAF protects against: SQL injection, XSS, CSRF, parameter tampering, cookie poisoning, forceful browsing, bot traffic, and application-layer DoS.
→ F5 WAF Deep Dive: Application Security with ASM and Advanced WAF
APM — Access Policy Manager
APM is F5’s identity and access module — where F5 moves beyond traffic delivery into access control.
- SSL VPN — full network-level remote access via BIG-IP Edge Client, comparable to Cisco AnyConnect or Fortinet SSL VPN
- Zero Trust Network Access (ZTNA) — identity-aware, per-application access without exposing the full network
- SSO — Kerberos, SAML, OAuth integration for seamless authentication across applications
- MFA integration — RADIUS, LDAP, Active Directory, RSA SecurID
- Endpoint inspection — verifying device health (AV status, patch level, domain membership) before granting access
APM’s advantage over standalone VPN solutions: it shares the same hardware and management plane as LTM. One platform for both application delivery and remote access.
AFM — Advanced Firewall Manager
AFM adds network-level firewall capabilities to the F5 platform:
- L3/L4 stateful packet inspection — similar to a traditional network firewall, running inline on the ADC
- DoS and DDoS protection — rate limiting, protocol anomaly detection, TCP SYN flood mitigation at hardware speeds
- IP intelligence — blocking known-bad IPs, Tor exit nodes, botnet C2 addresses via F5’s threat intelligence feeds
- Network Address Translation (NAT) policies
AFM is deployed when organizations want to consolidate firewall and ADC functions on a single platform, or when the ADC itself needs a dedicated protection layer.
BGP and Dynamic Routing
One of the least-known F5 capabilities: BIG-IP runs a full routing stack.
TMOS supports BGP, OSPF, static routes with route domains (VRF-equivalent), and ECMP. In practice, BGP is the most relevant:
- F5 can participate in BGP routing and advertise Virtual IP addresses as BGP routes
- In large enterprise and service provider environments, anycast VIP advertisement via BGP allows the same VIP IP to be advertised from multiple data centers — routing naturally directs clients to the nearest healthy site
- BGP withdrawal during maintenance windows automatically shifts traffic to DR sites without manual DNS changes
In the banking environment I worked in, we used BGP between F5 and the core routing layer to dynamically withdraw VIP advertisements during planned maintenance — clean, automatic, no DNS changes required.
Link Controller
Link Controller manages outbound internet connectivity across multiple ISP links:
- Load balancing across multiple upstream ISP connections
- Cost-based routing — prefer cheaper links, fail over to premium links when needed
- ISP health monitoring with automatic rerouting on link failure
Most relevant for organizations with multiple ISP connections that want intelligent distribution rather than simple active-standby.
iRules and iRules LX
iRules are F5’s programmable traffic layer — Tcl-based scripts that execute in the TMOS data plane at wire speed. They apply across modules and can manipulate any aspect of traffic: headers, URIs, cookies, routing decisions, SSL attributes.
iRules LX extends this with a Node.js runtime for more complex logic and external API integrations.
iRules are what make F5 uniquely flexible for organizations with non-standard application requirements — when no profile or policy covers the use case, an iRule usually can.
When Does F5 Make Sense — and When Doesn’t It?
F5 BIG-IP is powerful, operationally mature, and expensive. The decision to deploy it should be based on specific requirements, not on reputation alone.
F5 is the right choice when:
- SSL/TLS termination volume is high — hardware acceleration on physical appliances handles thousands of sessions per second that software solutions cannot match economically
- Applications require complex traffic logic (iRules) that simpler proxies cannot express without application code changes
- Multiple data centers require automated DNS-level failover (GTM)
- Regulatory requirements mandate WAF with detailed audit logging
- You need a single platform for application delivery, VPN, and L7 security — reducing operational complexity
- Mission-critical applications need sub-second HA failover with connection state mirroring
Consider alternatives when:
- Your infrastructure is fully cloud-native — AWS ALB, Azure Load Balancer, or GCP Load Balancing cover most use cases without on-premises hardware
- Traffic volumes are moderate and Nginx Plus or HAProxy handle your requirements at a fraction of the cost
- Applications are stateless and session persistence is not required
- TCO is the primary constraint and open-source solutions are operationally feasible for your team
The honest summary: in banking, telco, and large enterprises with on-premises infrastructure and mission-critical application requirements, F5 remains the dominant platform. In cloud-native or cost-constrained environments, evaluate alternatives seriously before committing to F5 licensing.
This Series
This article is the starting point. Each module has a dedicated deep dive:
- 🔧 F5 LTM Deep Dive: Virtual Servers, iRules, SSL Offloading & HA — Full-proxy architecture, pool configuration, health monitors, iRule examples, session persistence, HA clustering, and a zero-downtime 30-device migration walkthrough
- 🌐 F5 GTM & GSLB Deep Dive: Global Traffic Management and DNS Failover — Wide IPs, iQuery, topology routing, TTL strategy, active-active vs. active-standby DC patterns
- 🛡️ F5 WAF Deep Dive: Application Security with ASM and Advanced WAF — Security policy models, OWASP Top 10 coverage, bot defense, L7 DoS protection, and transparent-to-blocking deployment strategy
Related Articles
- 🛡️ Network Packet Broker (NPB) Masterclass — Traffic visibility across the full stack
- 🔐 The Zero Trust Mindset: Engineering Security as an Architecture — Where APM and WAF fit in Zero Trust
- 🏗️ IT Infrastructure Is Not a Collection of Products — Systems thinking behind ADC placement
- 🎯 Network Infrastructure Product Selection: Strategic Criteria — How to evaluate ADC vendors objectively